Generate Private Key Wildcard Certificate
In fact, the process for generating wildcard CSR is the same as any other CSR, with one key difference. However, before we show you how to generate CSR for wildcard certificate, the following is a brief intro to CSRs in general. The CSR (Certificate Signing Request) is essentially an application to be issued an SSL certificate. Get started with Key Vault certificates.; 4 minutes to read +7; In this article. The following scenarios outline several of the primary usages of Key Vault’s certificate management service including the additional steps required for creating your first certificate in your key vault.
-->The following scenarios outline several of the primary usages of Key Vault’s certificate management service including the additional steps required for creating your first certificate in your key vault.
The following are outlined:
- Creating your first Key Vault certificate
- Creating a certificate with a Certificate Authority that is partnered with Key Vault
- Creating a certificate with a Certificate Authority that is not partnered with Key Vault
- Import a certificate
Certificates are complex objects
Certificates are composed of three interrelated resources linked together as a Key Vault certificate; certificate metadata, a key, and a secret.
Creating your first Key Vault certificate
Before a certificate can be created in a Key Vault (KV), prerequisite steps 1 and 2 must be successfully accomplished and a key vault must exist for this user / organization.
Step 1 - Certificate Authority (CA) Providers
- On-boarding as the IT Admin, PKI Admin or anyone managing accounts with CAs, for a given company (ex. Contoso) is a prerequisite to using Key Vault certificates.
The following CAs are the current partnered providers with Key Vault:- DigiCert - Key Vault offers OV TLS/SSL certificates with DigiCert.
- GlobalSign - Key Vault offers OV TLS/SSL certificates with GlobalSign.
Step 2 - An account admin for a CA provider creates credentials to be used by Key Vault to enroll, renew, and use TLS/SSL certificates via Key Vault.
Step 3 - A Contoso admin, along with a Contoso employee (Key Vault user) who owns certificates, depending on the CA, can get a certificate from the admin or directly from the account with the CA.
- Begin an add credential operation to a key vault by setting a certificate issuer resource. A certificate issuer is an entity represented in Azure Key Vault (KV) as a CertificateIssuer resource. It is used to provide information about the source of a KV certificate; issuer name, provider, credentials, and other administrative details.
Ex. MyDigiCertIssuer
- Provider
- Credentials – CA account credentials. Each CA has its own specific data.
For more information on creating accounts with CA Providers, see the related post on the Key Vault blog.
Step 3.1 - Set up certificate contacts for notifications. This is the contact for the Key Vault user. Key Vault does not enforce this step.
Note - This process, through step 3.1, is a onetime operation.
Creating a certificate with a CA partnered with Key Vault
Step 4 - The following descriptions correspond to the green numbered steps in the preceding diagram.
(1) - In the diagram above, your application is creating a certificate which internally begins by creating a key in your key vault.
(2) - Key Vault sends an TLS/SSL Certificate Request to the CA.
(3) - Your application polls, in a loop and wait process, for your Key Vault for certificate completion. The certificate creation is complete when Key Vault receives the CA’s response with x509 certificate.
(4) - The CA responds to Key Vault's TLS/SSL Certificate Request with an X509 TLS/SSL Certificate.
(5) - Your new certificate creation completes with the merger of the X509 Certificate for the CA.
Key Vault user – creates a certificate by specifying a policy
Repeat as needed
Policy constraints
- X509 properties
- Key properties
- Provider reference - > ex. MyDigiCertIssure
- Renewal information - > ex. 90 days before expiry
A certificate creation process is usually an asynchronous process and involves polling your key vault for the state of the create certificate operation.
Get certificate operation- Status: completed, failed with error information or, canceled
- Because of the delay to create, a cancel operation can be initiated. The cancel may or may not be effective.
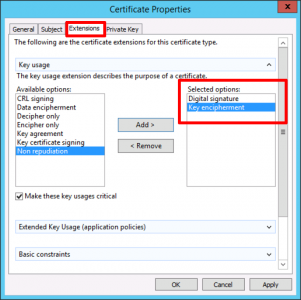
Private Key Definition
Import a certificate
Alternatively – a cert can be imported into Key Vault – PFX or PEM.
Import certificate – requires a PEM or PFX to be on disk and have a private key.
You must specify: vault name and certificate name (policy is optional)
PEM / PFX files contains attributes that KV can parse and use to populate the certificate policy. If a certificate policy is already specified, KV will try to match data from PFX / PEM file.
Once the import is final, subsequent operations will use the new policy (new versions).
If there are no further operations, the first thing the Key Vault does is send an expiration notice.
Also, the user can edit the policy, which is functional at the time of import but, contains defaults where no information was specified at import. Ex. no issuer info
Fable III is the next blockbuster installment in the highly praised Fable franchise. It’s a Revolution! Fable 3 product key generator skidrow.
Formats of Import we support
We support the following type of Import for PEM file format. A single PEM encoded certificate along with a PKCS#8 encoded, unencrypted key which has the following
-----BEGIN CERTIFICATE----------END CERTIFICATE-----
-----BEGIN PRIVATE KEY----------END PRIVATE KEY-----
On certificate merge we support 2 PEM based formats. You can either merge a single PKCS#8 encoded certificate or a base64 encoded P7B file.-----BEGIN CERTIFICATE----------END CERTIFICATE-----
We currently don't support EC keys in PEM format.
Creating a certificate with a CA not partnered with Key Vault
This method allows working with other CAs than Key Vault's partnered providers, meaning your organization can work with a CA of its choice.
The following step descriptions correspond to the green lettered steps in the preceding diagram.
(1) - In the diagram above, your application is creating a certificate, which internally begins by creating a key in your key vault.
(2) - Key Vault returns to your application a Certificate Signing Request (CSR).
(3) - Your application passes the CSR to your chosen CA.
(4) - Your chosen CA responds with an X509 Certificate.
(5) - Your application completes the new certificate creation with a merger of the X509 Certificate from your CA.
SSL Certificate CSR Creation for F5 BIG-IP
If you already have your SSL Certificate and just need to install it, see
SSL Certificate Installation :: f5 BIG-IP.
How to generate a CSR using an F5 BIG-IP Loadbalancer (version 9)
- Launch the F5 BIGIP web GUI.
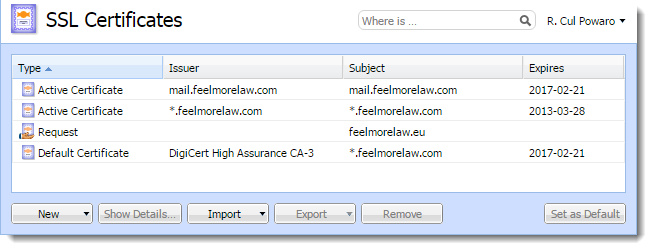
- Under Local Traffic select 'SSL Certificates' then 'Create.'
- Under General Properties give your certificate a name (this name will be used in the future to identify this certificate).
Under Certificate Properties enter the following information:
Issuer: Certificate Authority (DigiCert)
Common name: FQDN (fully-qualified domain name) of the server (e.g., www.domain.com, mail.domain.com, or *.domain.com)
Division: Your department, such as 'Information Technology'
Organization: The full legal name of your organization (e.g., DigiCert Inc)
Locality, State or Province, Country: City, state, and country where your organization is located
E-mail Address: Your email
Challenge Password, Confirm Password: Your password
- Under 'Key Properties', choose 2048.
Click the Finished button.
You should now be provided with the text of a Certificate Signing Request file. You will want to copy and paste the entire body of that file into the DigiCert order process when prompted.
After you receive your SSL Certificate from DigiCert, you can install it.
See SSL Certificate Installation :: f5 BIG-IP.
CSR Generation (Earlier versions of Big-IP)
First, login to the BIG-IP device as the root user and run the following command:
# /usr/local/bin/genconfYou will be asked to enter your company details including the full legal company name and address of operation.
You can now make your Certificate Signing Request by entering the following command:
# /usr/local/bin/genkey www.yoursite.comMake sure to replace 'www.yoursite.com' with the Fully Qualified Domain Name of the site that you are securing. You will again be asked to enter your company details.
Under /config/bigconfig/ssl.csr/ you will find a new file named your www.yoursite.com.csr -- This is your new CSR file. Transfer it to the workstation you will use to order the certificate. The CSR file can be opened with a text editor such as Notepad. Copy and paste the contents of the CSR file to the DigiCert order form. Make sure to include the BEGIN and END tags.
After you receive your SSL Certificate from DigiCert, you can install it.
See SSL Certificate Installation :: f5 BIG-IP.
f5 SSL Certificates, Guides, & Tutorials
Godaddy Wildcard Certificate
Buy NowLearn MoreGenerating a CSR for Issuance of an SSL Certificate in BIG-IP
How to generate an SSL Certificate Signing Request for your F5 BIG-IP Loadbalancer